In the ever-evolving landscape of cybersecurity, 0day Onion emerges as a critical concern for software developers and network administrators alike. The term "0day" refers to vulnerabilities that are exploited before the vendor has released a patch, while "Onion" connects to the anonymity provided by the Tor network. This combination underscores the challenges faced by those trying to secure their systems against unforeseen threats.
Understanding 0day Vulnerabilities
- This is a collection of important onion sites that you can leverage for Deepweb and Darkweb Monitoring
- Both red and blue teams benefit from a curated database that includes CVE to exploit mappings.
- Viruses, ransomware, and other types of malware are more common on onion sites than on the normal internet.
- If you’re reading this guide and learning new sysadmins tricks, my best advice is that you should probably stay away from darknet entrepreneurship (especially darknet markets and all form of illegal activities online).
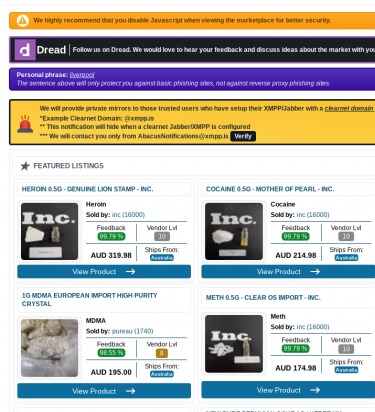
- The emergence of platforms like 0day onion underscores the increasing complexity of tackling illicit activities conducted anonymously through encrypted networks and dark web domains.
- As discussions evolve, trends emerge around new vulnerabilities and the tools that can be used to manipulate them.
The 0day vulnerabilities represent a unique risk; they can be leveraged by attackers to gain unauthorized access or cause significant disruptions before any defensive measures have been deployed. Unlike conventional threats, these vulnerabilities are often unknown to the software developers and security experts until they are exploited.
How 0day Onion Works
The 0day Onion references the dark web, where unrestricted discussions and sales of vulnerabilities take place. In this hidden part of the internet, hackers share detailed information about 0day exploits. This creates a marketplace where such critical vulnerabilities can be bought and sold, often to the highest bidder, making the task of securing systems even more daunting.

The lifecycle of a zero-day begins with its discovery, either by security researchers, attackers, or the vendor itself. They can be used to deploy ransomware, steal sensitive data, or establish long-term access to a compromised system. This window of unmitigated risk, from discovery by malicious actors to the development and deployment of a fix, is the defining characteristic of a zero-day threat.
The Impact on Cybersecurity
One of the most alarming aspects of 0day Onion is how quickly these vulnerabilities can be weaponized. A single vulnerability exposed on forums can lead to widespread attacks, as cybercriminals often act swiftly to exploit weaknesses. Organizations that fail to keep their systems updated and monitor such threats remain particularly vulnerable. The need for proactive security measures has never been more pressing, as the 0day market continues to grow.
Prevention Strategies
To combat the threats posed by 0day vulnerabilities, organizations can adopt a variety of strategies. First, implementing real-time monitoring systems can help detect unusual anomalies within the network. Regular software updates and comprehensive security audits are also crucial in mitigating risks associated with 0day Onion exploits.
Educating Teams
Another vital component is training personnel about cybersecurity best practices. Awareness of 0day threats and potential attack vectors can significantly enhance an organization's resilience against such vulnerabilities. Team members should know how to report suspicious activity and ensure that everyone understands the value of timely software updates.
The Future of 0day Onion
The landscape of 0day Onion vulnerabilities is continuously shifting. As cybersecurity measures evolve, so do the methods employed by attackers. Staying ahead in this game requires constant vigilance and an adaptive approach to security. While it's impossible to eliminate all risks, the implementation of robust security measures can dramatically minimize the impact these vulnerabilities may have.
Ultimately, understanding the complexities of 0day vulnerabilities and the role of the dark web—where the 0day Onion thrives—is essential in creating a secure digital environment. Ongoing education, proactive security practices, and a commitment to resilience will remain the cornerstones of effective cybersecurity in the years to come.